







































Drift Protocol Exploit Hits $285M in Suspected DPRK-Linked Attack
 DRIFT
DRIFT
 SOL
SOL
 DEFI
DEFI
 MM
MM
 READ
READ
Attackers drained approximately $285 million from Solana-based Drift Protocol on April 1, 2026, in what blockchain forensics firms describe as a governance compromise operation bearing hallmarks of suspected North Korean tradecraft, not a conventional smart contract exploit.
Drift Protocol confirmed the incident in a post on X, stating that it was experiencing an active attack and had suspended all deposits and withdrawals. The protocol, one of the larger perpetual futures platforms on Solana, went dark within minutes of the first unauthorized transfers.
How Attackers Drained $285 Million in 12 Minutes
Blockchain intelligence firm TRM Labs said the attackers drained roughly $285 million from Drift in approximately 12 minutes. Most of the stolen funds were bridged to Ethereum within hours of the exploit.
Elliptic, a separate blockchain forensics firm, estimated the losses at about $286 million, with the discrepancy reflecting differences in asset valuation timing across the two firms. Elliptic identified the largest single stolen transfer as approximately 41.7 million JLP tokens worth roughly $155 million at the time of theft.
The speed of the operation distinguishes it from slower, multi-stage exploits. Drift's immediate suspension of deposits and withdrawals limited further exposure, but the bulk of damage was already done before the shutdown took effect.
Why Investigators Point to DPRK Tradecraft, Not a Code Bug
TRM Labs said the critical failure was not a vulnerability in Drift's smart contracts. Instead, the exploit relied on a combination of social engineering targeting multisig signers, pre-signed durable nonce transactions, and a zero-timelock Security Council migration that allowed the attackers to bypass standard governance delays.
This distinction matters. A smart contract bug implies a flaw in the protocol's code that can be patched. What investigators described here is a governance and signer compromise, a fundamentally different attack surface that raises questions about how DeFi protocols secure their administrative keys and upgrade paths.
Elliptic said the on-chain laundering behavior and network-level indicators were consistent with prior DPRK-linked operations. The rapid cross-chain movement of funds from Solana to Ethereum mirrors patterns seen in earlier incidents attributed to North Korean groups.
However, no public government or law-enforcement attribution confirming DPRK responsibility has been issued. The suspected link remains based on private-sector analysis of behavioral and technical indicators, not official confirmation. Readers following evolving regulatory frameworks around digital asset compliance in Japan and other jurisdictions will recognize the difficulty of formal state-level attribution in crypto-related incidents.
Drift's TVL Collapsed to Under $8 Million
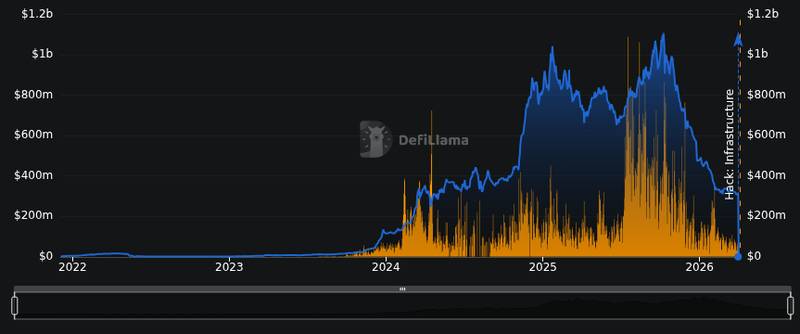
The impact on Drift's platform standing has been severe. DeFiLlama data shows Drift Trade with approximately $7.76 million in total value locked on Solana after the exploit, a catastrophic decline for a protocol that previously held hundreds of millions in user deposits.
The DRIFT token was trading at roughly $0.0473 with a market capitalization of about $27.5 million, according to CoinGecko data. Despite a 6.4% bounce over the prior 24 hours, the token remains under heavy pressure as markets assess whether the protocol can recover user trust.
The incident adds to a difficult period for risk assets broadly. The broader crypto market has already been navigating geopolitical uncertainty, and the Fear and Greed Index sat at 9, deep in Extreme Fear territory, at the time of the exploit.
Compliance Exposure for Bridges and Exchanges
If the DPRK attribution holds, the incident carries sanctions-screening implications for every intermediary the stolen funds touched. The U.S. government has previously linked North Korean crypto theft to weapons-program funding, which means exchanges, bridges, and on-ramps that process transactions tied to the stolen addresses face potential compliance exposure.
Elliptic noted that the laundering path, moving assets rapidly from Solana to Ethereum, places particular scrutiny on cross-chain bridge operators. The current macroeconomic environment already has regulators focused on financial system integrity, and a nine-figure theft with suspected state-actor involvement is likely to intensify that attention.
Drift has not yet published a full public postmortem. The protocol's initial statement confirmed the attack and service suspension but did not detail the complete exploit mechanics or outline a recovery plan. Until that postmortem arrives, the blockchain forensics reports from TRM Labs and Elliptic remain the most detailed public accounts of how the attack unfolded.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.
Read original article on kanalcoin.com
